-
Business

7 Steps to Small Business Marketing Success
Catch the Full Episode Overview At 20 years, younger business marketing he went down to one question: can google find…
Read More » -
Finance
Social Security COLA Forecasts Rise As Monetary Strength Increases
We research all the brands listed and may earn payment from our partners. Research and financial considerations may influence how…
Read More » -
Finance

5 Monthly Bills to Consider for a Comfortable Retirement
We research all the brands listed and may earn payment from our partners. Research and financial considerations may influence how…
Read More » -
Finance

Why You Can Give a Bank Free Money
We research all the brands listed and may earn payment from our partners. Research and financial considerations may influence how…
Read More » -
Finance

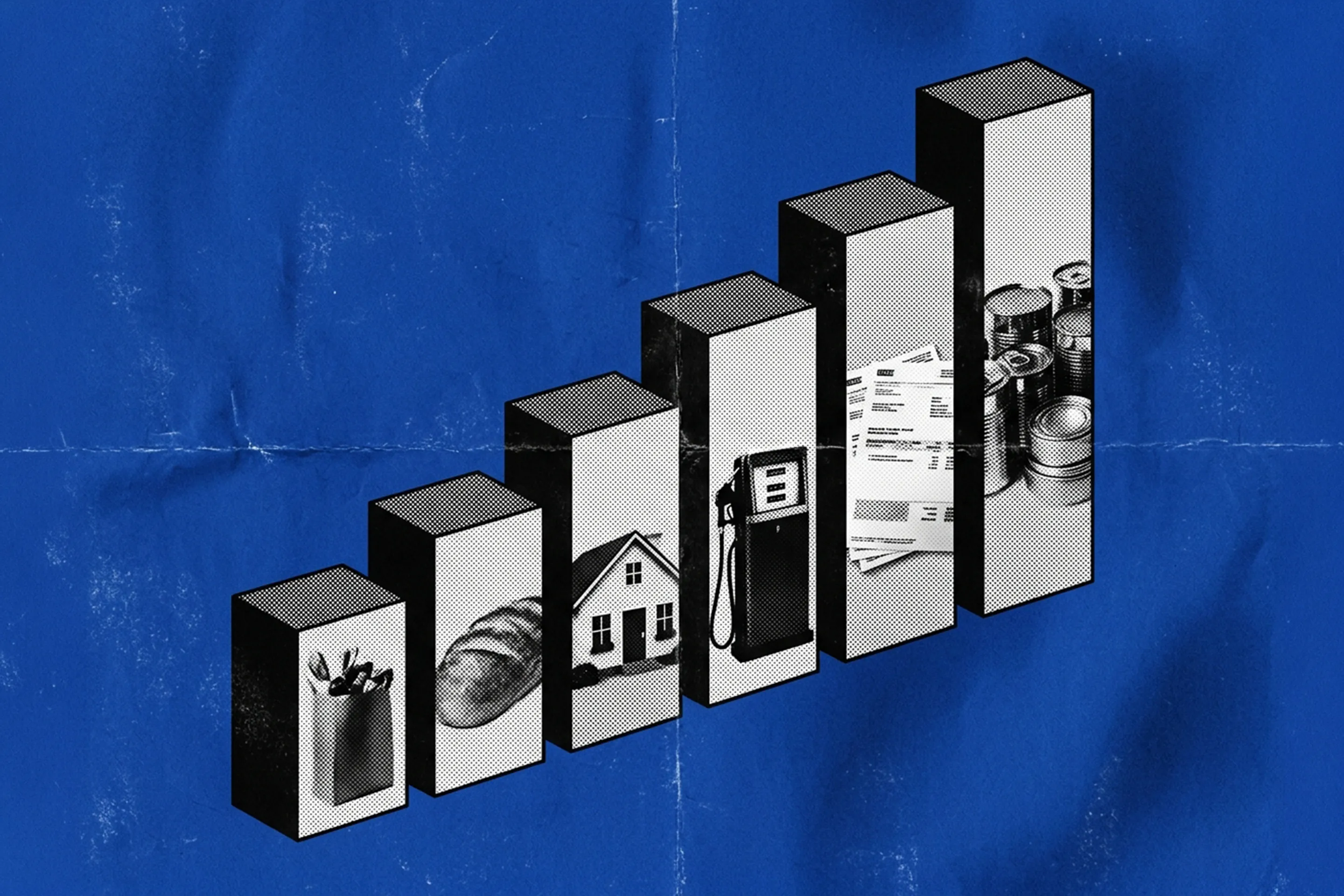
Income, Market & Asset Trends
When a business changes hands, a patent is licensed, or an investment portfolio is stress tested, one question immediately arises:…
Read More » -
Technology

What skills will give you an edge in the Industry 4.0 space?
Industry 4.0 represents an opportunity for emerging, ambitious and future-oriented professionals to change the world as we know it. The…
Read More » -
Finance

What is a Prop Trading Firm? Structure, Risk and Growth Explained
Proprietary trading gets a lot of attention because, from the outside, the model sounds straightforward: the company trades on its…
Read More » -
Business

Max Levchin, PayPal and Affirm — The Road from the Soviet Union to the Creation of Multibillion-Dollar Corporations (Also: Real-World Socialism vs. Capitalism) (#869)
Max Levchin (@mlevchin) is an entrepreneur, computer scientist, philanthropist, and active investor in over 100 startups. He is the founder…
Read More » -
Business

The Back of the Marketing Hourglass Is Where the Real Growth Is
The Marketing Hourglass has 7 stages: Know, Love, Trust, Try, Buy, Repeat, Refer. Most small businesses have five startup plans.…
Read More » -
Digital Marketing

Marketing needs AI results, not more AI pilots
Marketing teams are under increasing pressure to prove that AI can deliver real value, such as generating revenue, achieving machine…
Read More »